6 Ways to Improve Defense and Aerospace CyberSecurity

It’s the underlying message of every superhero movie: as the strength of the “good guy” increases, the power of the “bad guys” rises to meet it. Every time a new hero straps on his cape, some supervillain comes blazing on the scene with a chip on his shoulder and futuristic weapon in his hand.
In a caricature-esque way, this illustrates a real principle: as unprecedented opportunities arise, so do unexplored challenges and risks.
That is why, with an ever-increasing focus on innovation, it is more important than ever that aerospace and defense (A&D) companies develop strategic plans to increase digital and physical security. Defense and aerospace cybersecurity should be top of mind.
Traditionally, aerospace and defense has been a highly risk-averse industry. After all, individual lives and national safety all rest on the efficiency of security strategies and processes. But now, with an uptick in the demand for military equipment and global increase in defense budgets, the appetite for innovation is sure to follow.
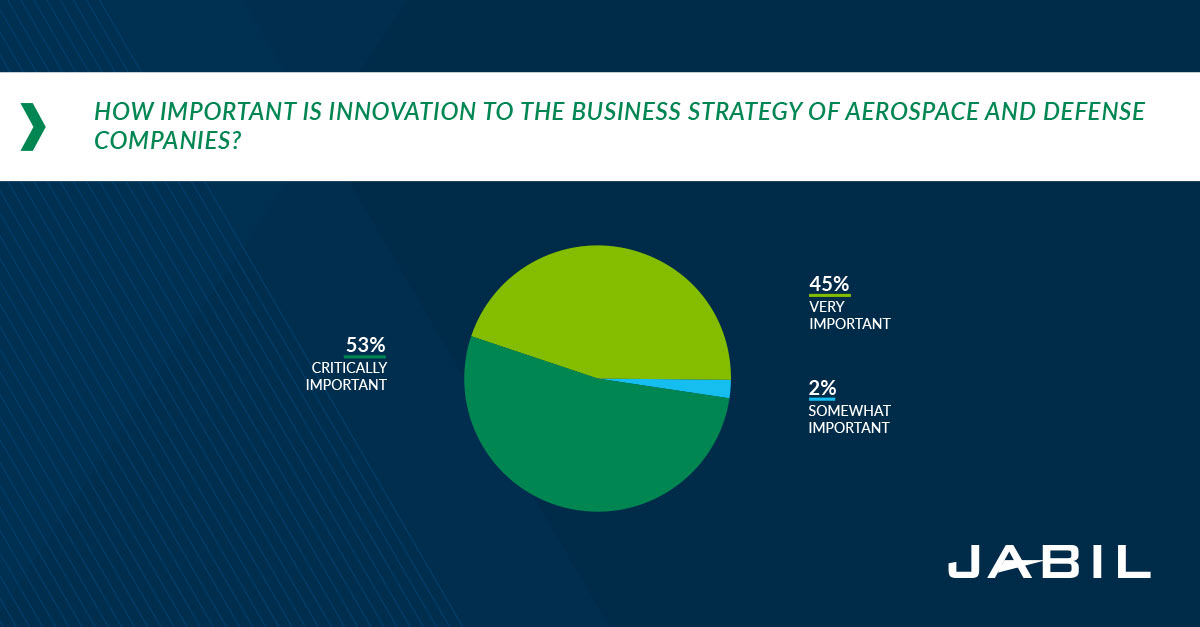
Not only could clinging to the old prove detrimental to national security, but many new technical solutions, such as automation and artificial intelligence, are designed to make commercial air travel safer. In Jabil’s recent Aerospace and Defense Manufacturing Trends survey, over half of the participants said that innovation is “critically important for their company’s ongoing business strategy." Download the full survey report.
Airplanes are being fitted with artificial intelligence. Weapons are being upgraded with intelligence, surveillance and reconnaissance systems. Data is being gathered and stored in unprecedented quantities. But while these new capabilities are designed to increase safety and efficiency, they also open new vulnerabilities in aerospace cybersecurity.
Governments across the world are taking action to establish and accelerate cybersecurity measures, for both the commercial and military sectors. In 2016, the U.S. government allotted $14 billion to enhance cybersecurity systems and prevent cyberattacks from organized criminal gangs. Because of the looming threat of cyberattacks on weapon programs, that same year, the U.S. government earmarked $160 million to the Energy Department’s National Nuclear Security Administration for cyber-protection of weapon programs.
Globally, significant investments are being made in cloud network security solutions, which can be used for battlefield management, data protection and wireless security solutions. Other growing areas of cybersecurity include network security and cloud security software.
Still, it isn’t solely up to the government to ensure the security of the A&D industry. Aerospace and defense stakeholders need to evaluate their current physical and digital security strategies and determine how to respond to rising threats. Here are six tips for aerospace and defense companies to maximize their physical and digital security:
1. Make Security a Priority in Design
When you walk through your front door, you don’t think, “Oh, I’m so glad the electricity is working!” You just assume that when you flick the light switch, the correct terminals will open or close to direct the electricity running through the wires. Similarly, industry players and customers shouldn’t be impressed that their information and technology are secure. Security systems should eliminate problems before they’re even a blip on the radar. The best security system isn’t one that receives high praise for fending off a mammoth threat; it’s the one you don’t even know is there.
The best security system isn’t one that receives high praise for fending off a mammoth threat; it’s the one you don’t even know is there.
To borrow Benjamin Franklin’s axiom, “An ounce of prevention is worth a pound of cure.” By designing aircraft with security already top-of-mind, companies can prevent rearguard actions necessary to correct vulnerabilities that would have otherwise never existed if security had been more highly prioritized from the beginning.
As more threats are realized, the need to protect against them while aircraft are still being designed will be more and more important; if it isn’t already, digital and physical security will soon be the fourth critical measurement of an aerospace and defense company, along with cost, quality and schedule.
How Important is Innovation to the Business Strategy of Aerospace and Defense Companies?
Critically
Somewhat
Very Important
2. Converge Your Security Disciplines
In our Internet of Things-driven world, every company is now a software company, as Forbes declared as far back as 2011. The article stated, “The era of separating traditional industries and technology industries is over, and those who fail to adopt right now will soon find themselves obsolete.”
In 2019, this statement rings truer than when it was first written. Everything in our lives is becoming more connected; our refrigerators will text us to pick up milk, our coffeemakers will start as soon as our morning alarm goes off and cars will navigate and drive themselves. With revolutionary technology (like 5G networks) on the verge of becoming a reality, this trend will only grow.
Companies typically arrange their security disciplines in silos: physical security, cybersecurity (or IT security) and operational technology security. Unfortunately, these silos make it difficult to see the big picture; it’s like the old fable about a group of blind men who all formed entirely different ideas of what an elephant looked like based on the different parts they could feel. It interferes with visibility across security sectors. A disjointed approach ends up being costly, inefficient and leaves gaps for hackers to exploit.
A disjointed approach ends up being costly, inefficient and leaves gaps for hackers to exploit.
Currently, cybersecurity encompasses a variety of solutions: network, endpoint, application, content, cloud and wireless security solutions. Although each of these solutions can perform well individually, when melded together, they create a strong, multi-layered wall of defense against next-level threats.
Subscribe to the Jabil Blog
Sign up for weekly updates on the latest trends, research and insight in tech, IoT and the supply chain.
3. Hack Yourself
The reality of mid-air cyberattacks struck the aviation world in April 2015. A passenger onboard a flight tweeted that he had tapped into the plane’s operational systems by hacking the in-flight entertainment system. A subsequent FBI investigation revealed that the hacker claimed to have made a plane climb and move sideways on an earlier flight. Although experts later found these claims untrue, it did demonstrate how flight personnel are becoming increasingly reliant on digital controls and multiple networks, as well as how a hacker could override a plane’s operating system, steal data and more.
So, what can you do to prevent a malicious cyberattack? Hack yourself first.
A “white hat” security evaluation is one of the effective ways to pinpoint weaknesses in your security system. In fact, the U.S. Air Force instigated one of the first instances of white hat hacking to test its Multics operating system for potential use as a two-level (secret/top secret) system.
One of the most preeminent hacking events in the information security world is Pwn2Own. An annual tradition since 2007, cyberhackers compete for the chance to win cash prizes ranging from $35,000 to $250,000, depending on the exploit they use and the car system they target. Any security flaws exposed over the course of the contest are reported and later resolved.
Whether you create a competition, organize an in-house hackathon or hire a third-party to help, a friendly hack can help you locate holes in your systems and technologies before someone else does.
4. Create a Data “Tripwire”
According to our survey, in the last five years, aerospace and defense companies have invested in protecting customer data more than any other area of security. With medical devices storing healthcare information, retailers analyzing individuals’ shopping habits and even voice-activated assistants noting users’ habits at home, not to mention recent data breaches and privacy leaks, data privacy is a top-of-mind issue. Customers need to be able to trust that information won’t be used in ways they would not consent to. Additionally, on a more serious level, people poking into defense-related information may compromise national security.

If you read mystery books or watched detective cartoons growing up, you may be familiar with how a tripwire, such as a thread laid across a desk drawer, can be used as a simple trap to prove that someone is rifling through something they shouldn’t.
This same concept applies to information security: create a tripwire. Have systems in place so you know who is accessing data and – more importantly – if they’re supposed to be. And then ask questions; if someone works in finance, why are they accessing HR share? Or why is someone dedicated to Customer A digging into information on Customer B? There may be a legitimate and innocent explanation, but it’s better to understand the situation before an issue arises.
5. Communicate with Partners and Other Industry Players
In protecting data, it is vital to correctly and clearly classify data so everyone knows what degree of confidentiality it demands. Defense and aerospace stakeholders need to ensure that their partners understand the level of privacy so that companies they bring on board will be as careful with it as they are. Already, companies are making strides to make sure that everything they send forward is labeled so it can be properly addressed.
In addition to being conscious of the needs of specific documents and information, communicate with industry players outside your organization to remain aware of industry trends and news. There are several organizations founded by both governments and corporate enterprises designed to share industry information. These programs include:
- Aviation Information Sharing and Analysis Center (A-ISAC): Established in 2012 with backing from aircraft manufacturer Boeing, the A-ISAC describes itself as “a unique focal point for security information sharing across the aviation sector.” It aims to share security information with its community members, which consists of airlines, airports, aircraft manufacturers, equipment suppliers, service providers, technology providers, infrastructure providers and/or general aviation entities.
- Cyber Information Sharing and Collaboration Program (CISCP): Founded by the U.S. Department of Homeland Security, CISCP consists of government intelligence analysts, airline representatives and airport officials devoted to sharing security information across a variety of industries, including aerospace and defense.
6. Ensure Adequate Personnel Training
Currently, in the U.S., 1,500 hours of training are required for both pilots and co-pilots before they can take charge of a commercial aircraft. Internationally, the requirement is only 240 hours for copilots and can include a mix of simulators.
The idea behind the U.S.’s more stringent regulation is that experience equals safety; the more time pilots spend flying, the safer they, the crew and passengers will be. However, the emblem of reliable pilots is not merely that they’ve flown for many hours, but that during that time, they have experienced a variety of circumstances multiple times. Pilots and copilots must possess ample knowledge of how to fly in diverse weather conditions, understand new aviation technology and what to do in the event of different disasters and mishaps.
As automation and artificial intelligence mature and become more widespread, aviation training will not slacken; if anything, it will become more rigorous.
Already, autopilot and automation systems are an integral part of aircraft. According to government estimates, automated systems are activated 90 percent of a typical airline flight. However, some experts have expressed concern that these systems have interfered with pilots’ abilities to recognize and react to unexpected events.
There are numerous advantages to automation: its increased efficiency can save fuel; it helps pilots land in fog instead of diverting to another airport; and it can counteract poor judgment calls. However, flying instructors and trainers need to emphasize automation not as a replacement for manual flying skills but as a helpful aid.
Although it will not replace real-life flying experience, virtual and augmented reality will be key to improving training, allowing aviators to simulate various, realistic scenarios. In particular, it will allow them to experience different emergencies, allowing pilots and co-pilots to familiarize themselves with a disastrous situation, and administrators will be able to give constructive feedback and better determine if a pilot is qualified to navigate a crisis.
Digital and physical security is not something that the aerospace and defense industry can or does take lightly. Defense and aerospace cybersecurity directly impacts people’s lives and the state of the country, not to mention the country’s ability to protect itself, enforce its policies and protect both national and international investments. As technology advances, new threats will arise, but so will new safety features that can withstand these assaults and guide the aerospace and defense industry into a more efficient and – ultimately – safer future.
Download the Aerospace and Defense Manufacturing Trends Survey Report
Insights from over 200 aerospace and defense decision-makers at global enterprises on innovation, time-to-market, 3D printing, strategic plans and more.
